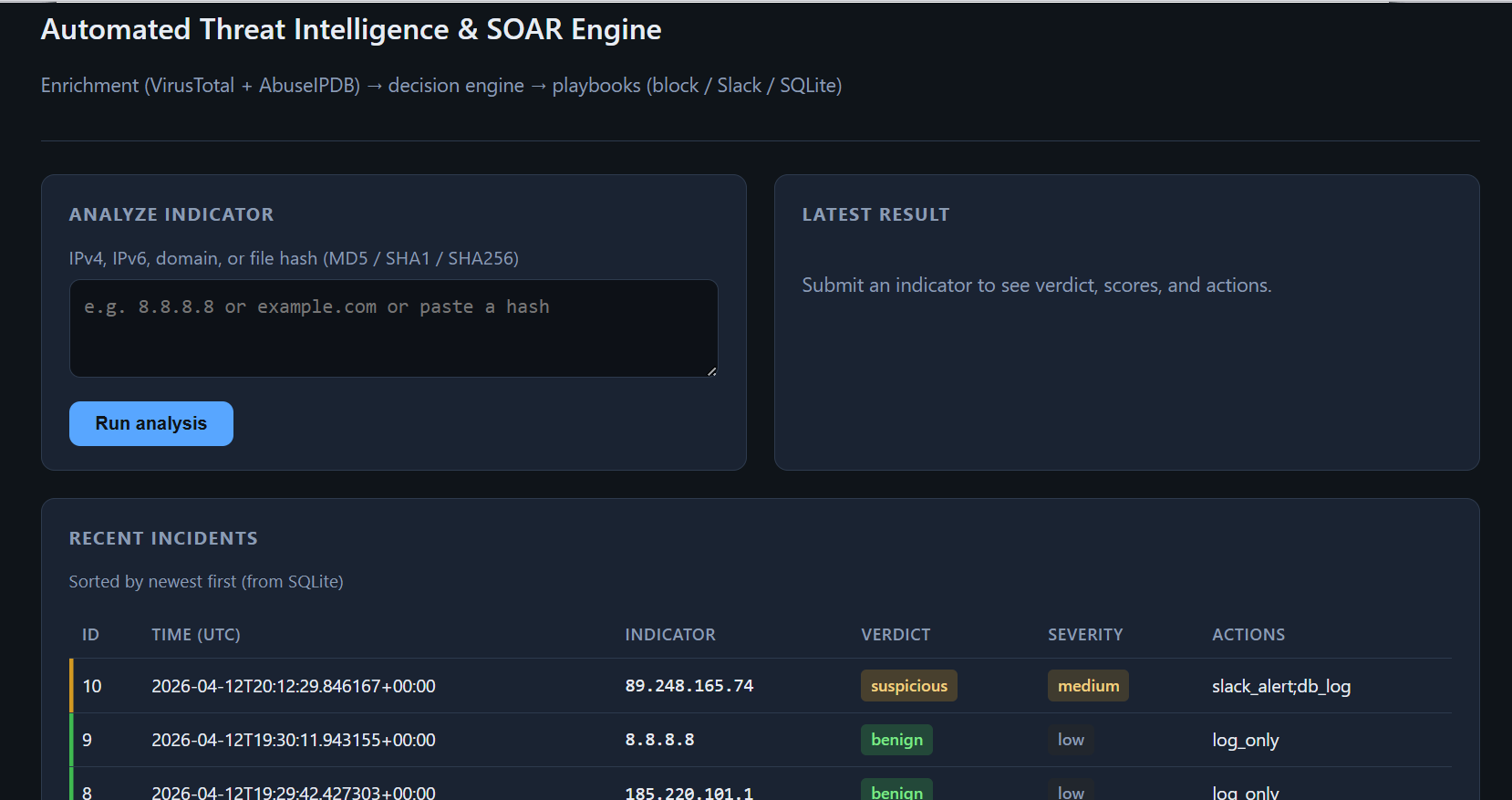
Automated Threat Intelligence & SOAR Engine
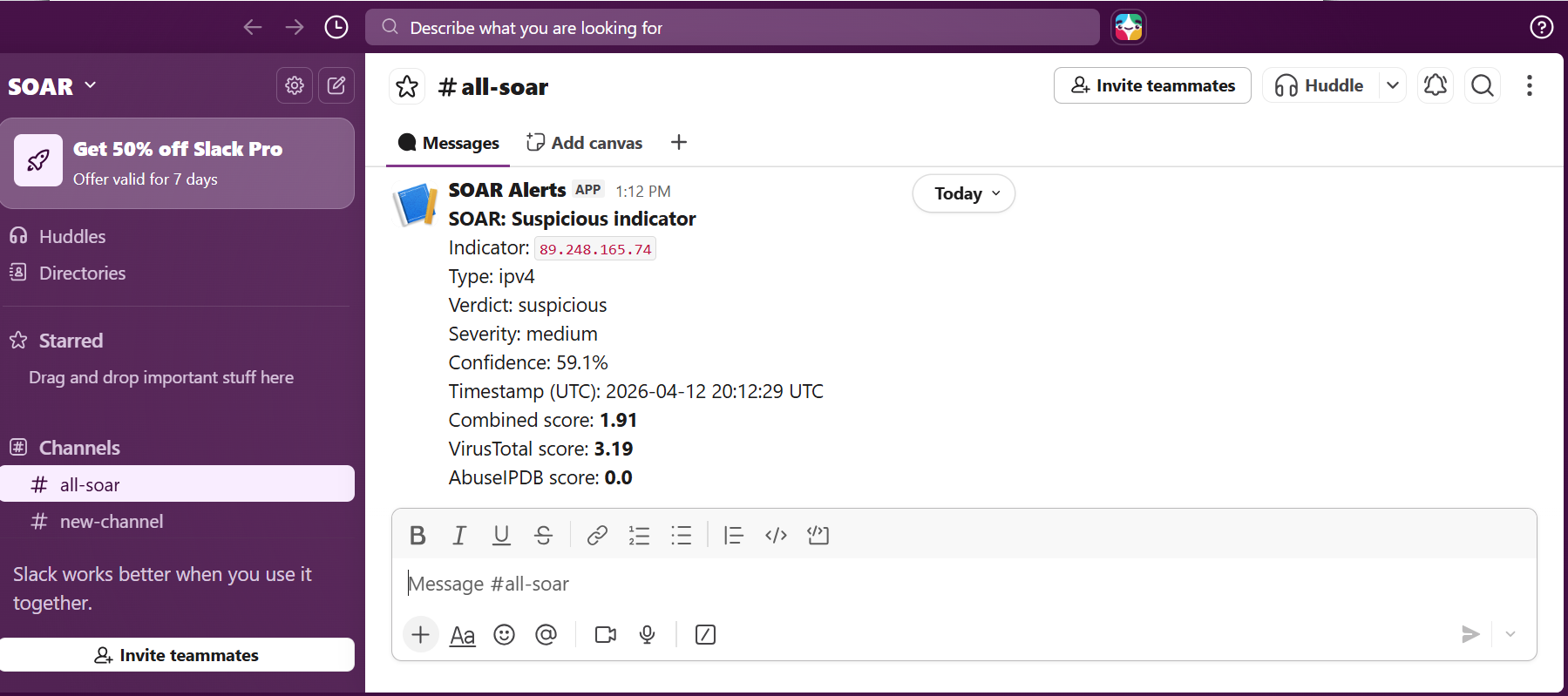
Security automation pipeline for Security Operations workflows: ingest IOC data (IP/domain/hash), enrich with threat intelligence, risk-score outcomes, and trigger alerting/playbook response steps for SOC analyst triage and incident handling.
Impact: Standardized enrichment, scoring, and alerting to reduce manual triage variance and improve analyst response consistency.
- ✓Threat intelligence enrichment via VirusTotal and AbuseIPDB
- ✓IOC triage workflow: ingest → enrich → risk score → incident handling action
- ✓Analyst-facing alerting and playbook-style response flow
- ✓Standardized API-driven scoring logic for consistent triage decisions